# General Methodo & Misc Tips
> Notes mostly from work and also from XSSrat course
## General Methodology
### Exploration and enumeration
* Read the documentation
* Explore the application
* **Inspect JS files** (you could find API key, hidden endpoint, hidden parameters, passwords etc.)
* Testing as unauthenticated
* Testing as user
* Testing as admin
* When doing web pentest it is always worth using checklist as there are so many things to test for. [Here](https://github.com/tanprathan/OWASP-Testing-Checklist) is one checklist
* Do not hesitate to tamper with responses also (not only requests)
* Test multiple injections at the same time with the following payload (SQLi, SSTi, CSTi, XSS)
```txt
'"`> ${7*7}
```
### Investigate Parameters
* Business logic erros
* IDORS
* CSRF tokens (check if it is present and test it if it exists)
* Parameter pollution (adding same parameter multiple times)
* Image upload: SVG for XXE
* Soap Request: XXE
* SQLi
* JWT tokens
* Unmapped object properties
* XSS
* Admin panel bypass
* Template injection
* Captcha bypass
## Install and use Chrome in kali
It can happen that an application is not made for firefox. In this case you will need another browser. Chrome could do the job.
* Intall Chrome
```bash
sudo apt update
wget https://dl.google.com/linux/direct/google-chrome-stable_current_amd64.deb
sudo apt install ./google-chrome-stable_current_amd64.deb
```
* Launch it with proxy and ignore cert errors `google-chrome-stable --proxy-server=127.0.0.1:8080 --ignore-certificate-errors` this way you will be able to see your request through burp as usual.
## Bypass Cert not private error on Chrome - Kali
***Warning: use we caution and only in your pentest environment/vm***\
Sometimes when you test a website you get an annoying error related to the certificates when you have to go back to it multiple times a day it can be a paint to click on ignore every time.\
Here is a quick fix for this
* In kali right click on Google Chrome and select Edit Application\
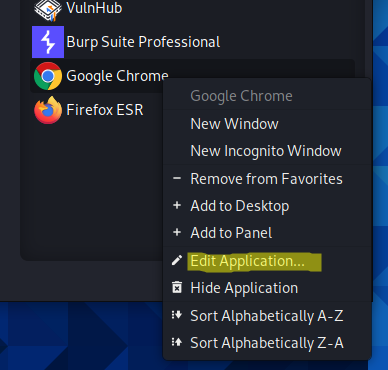
* At the end of "Command" add `--ignore-certificate-errors` and save, the command should look like this now:
```bash
/usr/bin/google-chrome-stable %U --ignore-certificate-errors
```
You can also use aliases if you prefer to launch everything with cmd.\
Here are the one I use (you have to add them in your .zshrc file or .bashrc file depending on the shell you use):
```bash
alias chromeburpnocert='google-chrome-stable --proxy-server=127.0.0.1:8080 --ignore-certificate-errors'
alias chromenocert='google-chrome-stable --ignore-certificate-errors'
alias chrome='google-chrome-stable'
```
## For whitebox test
### Git dorks
* When you are in whitebox you might get access to git repos. If for some reason you are not able to download the code, you can use git dorks to find specific strings
* `org:NameOfOrg keyword-in-repo-that-is-used-for-a-specific-project in:name,description,tags keyword-to-look-for` example `org:MyOrg myproject in:name,description,tags password`
## How to test for External service interaction without burp collaborator
Recently I had to check if I was able to trigger my target into sending dns request to random hosts. However I could not use burp collaborator.\
To replace it I used a great python tool that is similar to http simple server but for dns.\
This tool is called [dnserver](https://pypi.org/project/dnserver/)
### Install dnserver
```bash
sudo apt update
pip install dnsserver
```
### Launch dnserver
* `sudo python3 -m dnserver --port 5053 example_zones.toml` (if you use sudo you will have to put sudo in front of pip install dnserver for the install part)
* To test if you server works you can do this `dig @gabrielle.pwn -p 5053 gabrielle.pwn MX`
### Test if your target sends dns request to random hosts
Now you should be able to input your dns server where you need to and check if the app actually requests it. You can use wireshark or another tool to monitor the traffic.
## Useful resources for web pentest
{% embed url="" %}
Use Burp Suite and OWASP Zap at the same time by chaining proxy
{% endembed %}
* Foxyproxy
{% embed url="" %}
Chrome
{% endembed %}
{% embed url="" %}
Firefox
{% endembed %}
{% embed url="" %}
Containers only on Firefox
{% endembed %}
* I am more a Firefox user but when I have to use an alternate browser I use this extension it usually works pretty well. However the best method for Chrome, in my opinion, would be to use the new incognito window and allow foxyproxy in it, I find it more convenient.
{% embed url="" %}
Multi Login Firefox containers alternative for Chrome
{% endembed %}
{% embed url="" %}
Awesome Burp extensions - Snoopy Security
{% endembed %}
{% embed url="" %}
Payload all the things - swisskey repo
{% endembed %}
{% embed url="" %}
OWASP Cheat Sheet (useful for recommendations in report)
{% endembed %}
{% embed url="" %}
OWASP - Web Application Penetration Testing
{% endembed %}
{% embed url="" %}
Seclists
{% endembed %}
{% embed url="" %}
FuzzDB
{% endembed %}
{% embed url="" %}
OWASP Testing Checklist
{% endembed %}
{% embed url="" %}
OWASP Testing Guide
{% endembed %}
* This can be useful if you want to install apps to practice on
{% embed url="" %}
Install Docker on Kali
{% endembed %}
## Resources for practice
{% embed url="" %}
Practice with labs made by The XSS rat
{% endembed %}
{% embed url="" %}
Portswigger Web Security Academy
{% endembed %}
{% embed url="" %}
OWASP Juice Shop
{% endembed %}
{% embed url="" %}
Uncle rat's notes
{% endembed %}
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://csbygb.gitbook.io/pentips/web-pentesting/misc-tips.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.
${7*7}
```
### Investigate Parameters
* Business logic erros
* IDORS
* CSRF tokens (check if it is present and test it if it exists)
* Parameter pollution (adding same parameter multiple times)
* Image upload: SVG for XXE
* Soap Request: XXE
* SQLi
* JWT tokens
* Unmapped object properties
* XSS
* Admin panel bypass
* Template injection
* Captcha bypass
## Install and use Chrome in kali
It can happen that an application is not made for firefox. In this case you will need another browser. Chrome could do the job.
* Intall Chrome
```bash
sudo apt update
wget https://dl.google.com/linux/direct/google-chrome-stable_current_amd64.deb
sudo apt install ./google-chrome-stable_current_amd64.deb
```
* Launch it with proxy and ignore cert errors `google-chrome-stable --proxy-server=127.0.0.1:8080 --ignore-certificate-errors` this way you will be able to see your request through burp as usual.
## Bypass Cert not private error on Chrome - Kali
***Warning: use we caution and only in your pentest environment/vm***\
Sometimes when you test a website you get an annoying error related to the certificates when you have to go back to it multiple times a day it can be a paint to click on ignore every time.\
Here is a quick fix for this
* In kali right click on Google Chrome and select Edit Application\
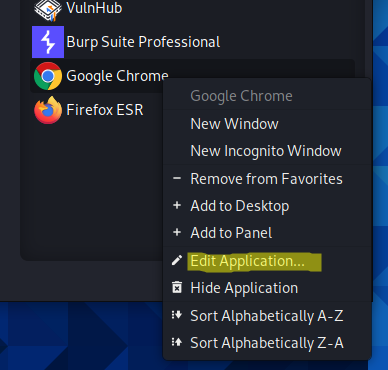
* At the end of "Command" add `--ignore-certificate-errors` and save, the command should look like this now:
```bash
/usr/bin/google-chrome-stable %U --ignore-certificate-errors
```
You can also use aliases if you prefer to launch everything with cmd.\
Here are the one I use (you have to add them in your .zshrc file or .bashrc file depending on the shell you use):
```bash
alias chromeburpnocert='google-chrome-stable --proxy-server=127.0.0.1:8080 --ignore-certificate-errors'
alias chromenocert='google-chrome-stable --ignore-certificate-errors'
alias chrome='google-chrome-stable'
```
## For whitebox test
### Git dorks
* When you are in whitebox you might get access to git repos. If for some reason you are not able to download the code, you can use git dorks to find specific strings
* `org:NameOfOrg keyword-in-repo-that-is-used-for-a-specific-project in:name,description,tags keyword-to-look-for` example `org:MyOrg myproject in:name,description,tags password`
## How to test for External service interaction without burp collaborator
Recently I had to check if I was able to trigger my target into sending dns request to random hosts. However I could not use burp collaborator.\
To replace it I used a great python tool that is similar to http simple server but for dns.\
This tool is called [dnserver](https://pypi.org/project/dnserver/)
### Install dnserver
```bash
sudo apt update
pip install dnsserver
```
### Launch dnserver
* `sudo python3 -m dnserver --port 5053 example_zones.toml` (if you use sudo you will have to put sudo in front of pip install dnserver for the install part)
* To test if you server works you can do this `dig @gabrielle.pwn -p 5053 gabrielle.pwn MX`
### Test if your target sends dns request to random hosts
Now you should be able to input your dns server where you need to and check if the app actually requests it. You can use wireshark or another tool to monitor the traffic.
## Useful resources for web pentest
{% embed url="" %}
Use Burp Suite and OWASP Zap at the same time by chaining proxy
{% endembed %}
* Foxyproxy
{% embed url="" %}
Chrome
{% endembed %}
{% embed url="" %}
Firefox
{% endembed %}
{% embed url="" %}
Containers only on Firefox
{% endembed %}
* I am more a Firefox user but when I have to use an alternate browser I use this extension it usually works pretty well. However the best method for Chrome, in my opinion, would be to use the new incognito window and allow foxyproxy in it, I find it more convenient.
{% embed url="" %}
Multi Login Firefox containers alternative for Chrome
{% endembed %}
{% embed url="" %}
Awesome Burp extensions - Snoopy Security
{% endembed %}
{% embed url="" %}
Payload all the things - swisskey repo
{% endembed %}
{% embed url="" %}
OWASP Cheat Sheet (useful for recommendations in report)
{% endembed %}
{% embed url="" %}
OWASP - Web Application Penetration Testing
{% endembed %}
{% embed url="" %}
Seclists
{% endembed %}
{% embed url="" %}
FuzzDB
{% endembed %}
{% embed url="" %}
OWASP Testing Checklist
{% endembed %}
{% embed url="" %}
OWASP Testing Guide
{% endembed %}
* This can be useful if you want to install apps to practice on
{% embed url="" %}
Install Docker on Kali
{% endembed %}
## Resources for practice
{% embed url="" %}
Practice with labs made by The XSS rat
{% endembed %}
{% embed url="" %}
Portswigger Web Security Academy
{% endembed %}
{% embed url="" %}
OWASP Juice Shop
{% endembed %}
{% embed url="" %}
Uncle rat's notes
{% endembed %}
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://csbygb.gitbook.io/pentips/web-pentesting/misc-tips.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.